Security is critical to your industrial operation. Specific measures should be implemented in order to make SCADA Systems and Industrial Control Systems (ICS) controlling critical infrastructure inherently more secure. Most likely, your SCADA or HMI software will come equipped with security features like username and password authentication for access to your network. Machines can access internet connections over secure thin clients, and web HMI interfaces for intelligent embedded systems can and should require unique credentials for users, with unique, complex passwords that change often.
With the rise in industrial cyber attacks growing exponentially and IBM estimating the typical financial impact of a single cyber attack at US $3.92 million, it makes sense to partner with a vendor who is committed to mitigating cybersecurity risk. As security threats become more complex, they become more difficult to prevent and detect. To protect your SCADA systems and HMIs, it’s worth looking into more advanced security solutions to fill any potential security gaps. AVEVA takes cybersecurity seriously, which is why all its cloud and on-premises offerings have security at their core.
In addition to its own native security features, AVEVA has partnered with leaders in the security industry to protect industrial systems from Edge to Enterprise. These partners have solutions to secure legacy and enterprise applications, cloud workloads, and even physical environments. Using these solutions will help keep your mission-critical applications up and running securely, and mitigate any physical breaches to sensitive data and industrial systems.


Longwatch Video Surveillance
A complete video monitoring solution that integrates into existing process control systems. Composed of industrial-grade software and video recording hardware along with a flexible ‘thin client’ viewer interface.

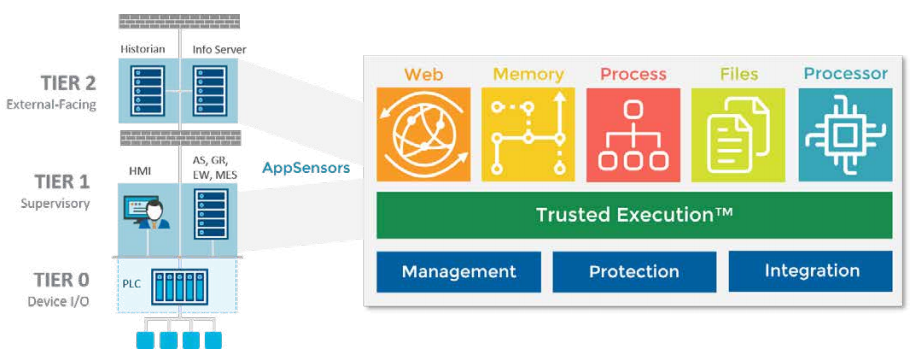
Virsec Security
Virsec Security Platform stops known and unknown threats across any application on any platform with unprecedented speed and accuracy. Virsec protects the entire attackable surface of the application — including Host, Memory, and Web layers — during runtime.