Helping you avoid risk, by protecting your investment
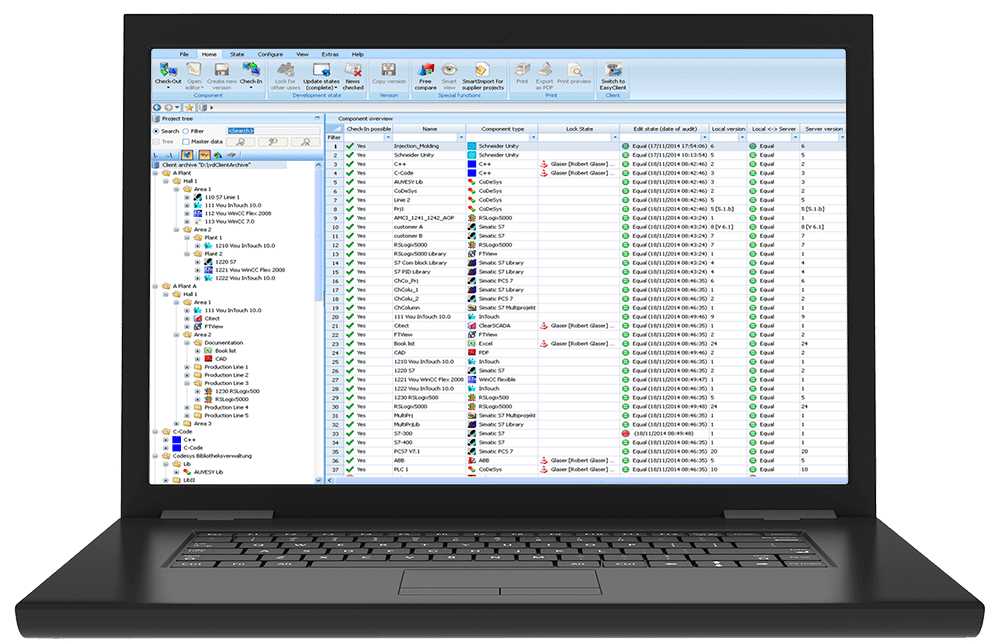
versiondog analyzes the automation device and system programming running across the plant floor using automated backup and compare functions to monitor, track and store changes. This synchronization between versiondog and plant systems enables the distribution and monitoring of company-wide technical standards and provides greater control, security and visibility into understanding the who, what, when, where and why of changes to automation devices and systems involved in manufacturing processes.
Companies invest a significant amount of money into the physical equipment that is used to run their processes, often times just as much, or more is spent on the automation programming that controls them. Does your company have a change management process in place to protect that investment?
Lacking clarity as to which programs are running on which devices at any given point can lead to real problems in automated production facilities. Finding the right version can be very time consuming and any confusion can have an adverse effect on quality, production volumes, or even cause line stoppage.
Features of versiondog
The versiondog system is a modern change management application specifically designed for today’s industrial automation. It brings a variety of features focused on improving equipment visibility, ease of use and security, while offering a simple installation process and maximum value to the business.
- Smart Compare – a simplified comparison process that does not require the vendor software.
- Permissions based clients – provides easy training and deployment for the various user access levels required.
- Non-connected Backup – utilize a laptop and physical cable to perform a backup for devices not on the network.
- Reporting – create and save on-demand reports based on tracked changes and other system data.
- Factory Floor Status – current status of the backup and compare jobs with results, based on the latest version
- Library Management – track changes of reusable blocks found in device standard libraries.
- Active Directory – simplify user management with direct integration to Microsoft Active Directory.

Components of automation change management
1 – Backup
versiondog can run on-demand or by schedule to automatically backup and secure all of your industrial automation programming. A centralized archive is used to manage each revision which ensures a complete history of the changes made. In the event of non-networked devices, the versiondog Backup Client can be used to capture and restore the programming of unconnected equipment.
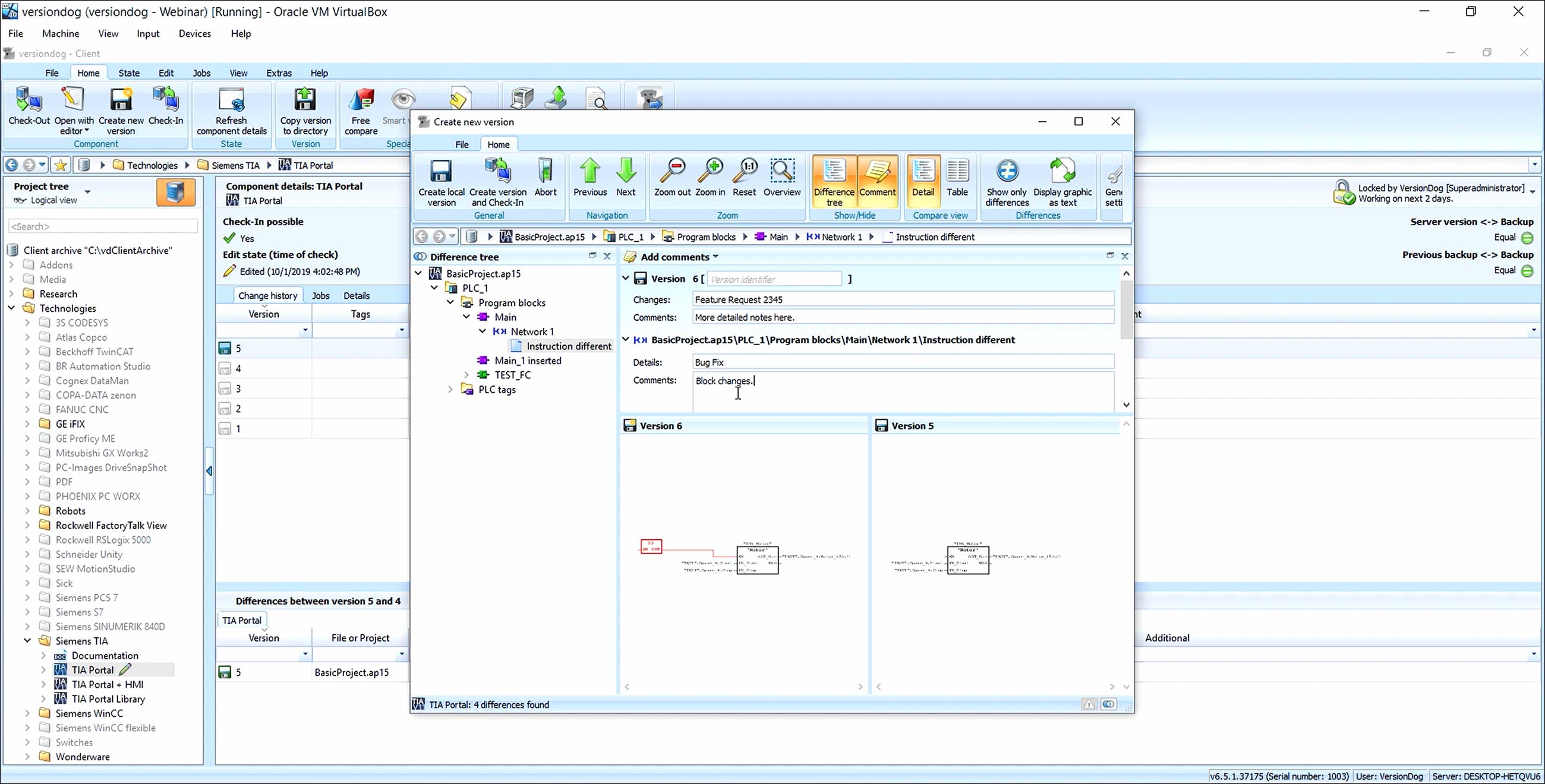
2 – Compare
Comparison can be done automatically with triggered alerts when changes are detected, or manually using a client. In most cases, the versiondog Smart Compare process does not require the vendor software, enabling a simplified comparison process. Detailed analysis can be done to drill down into graphical representations of the exact changes. In addition, compare reports can even be viewed independently of the automation equipment program for at-a-glance management review.
3 – Restore
In the event that a piece of equipment is damaged, or an unauthorized or bad change was made, versiondog can restore a previously saved revision of the program ensuring your process is returned to operation as quickly as possible. Saving time versus having to hunt through file directories or spreadsheets to track down the latest release.
4 – Audits, Analysis & Security
versiondog change management provides increased security to your industrial automation assets by securing the programs from alteration. User security can be assigned so that only authorized users have permission to modify automation programming. In addition, versiondog reporting provides detailed analysis of changes and supports documentation according to international standards such as ISO 900x, GMP, GAMP, VDA6.4 and FDA 21 CFR 11.
Time Savings
Change management brings organization to a traditionally unorganized activity. No longer do you need to track and store automation programs on various flash drives or manual spreadsheets. The task becomes entirely automated with versiondog, reducing wasted time spent managing change tracking and providing greater reliability and speed when a version needs to be recovered.
100% Traceability
Bring complete visibility to the programming change process. From the initial check-out process, through change documentation, audit logs and security, versiondog standardizes how changes are conducted, simplifying and structuring from start to finish. Whether you need to determine what was changed, who made the change or where this change is currently active – versiondog makes it easy.
Sustainability
Standardized processes are not new to industry. They exist in every aspect of a production process and yet technological changes don’t often get included. versiondog change management makes the act of tracking changes in industrial automation equipment a reliable and sustainable process, removing the variability and difficulty of traditional methods.
versiondog Supported Devices / Software
PLCs
- 3S CODESYS
- AEG
- B&R Automation Studio
- Beckhoff TwinCat
- BOSCH CPS21
- BOSCH Indralogic
- EATON
- ELAU
- GE Proficy ME
- Hitachi
- IBHsoftec S5 for windows
- IBHsoftec S7 for windows
- Mitsubishi GX Works2
- Mitsubishi GX Works3
- Phoenix CONTACT PC WORX
- Pilz
- Rockwell RSLogix5
- Rockwell RSLogix500
- Rockwell RSLogix5000
- Studio 5000 Logix Designer
- Schneider Concept
- Schneider EcoStructure Control Expert
- Schneider Modsoft
- Siemens Simotion
- Siemens STEP 5
- Siemens STEP 7
- Siemens TIA Portal with STEP 7
- WAGO e!cockpit
HMIs
- ABB Freelance
- AVEVA InTouch HMI (formerly Wonderware)
- AVEVA System Platform (formerly Wonderware)
- AVEVA Plant SCADA (formerly Citect)
- COPA-DATA Zenon
- GE CIMPLICITY
- GE Proficy iFix
- Rockwell FactoryTalk View ME/SE
- Siemens PCS7
- Siemens Protool
- Siemens WinCC
- Siemens WinCC flexible
CNC, Robots and more
- ABB
- COMAU
- FANUC
- Indramat
- Kawasaki
- KUKA
- MITSUBISHI
- OMRON Adept
- SEW
- Siemens SINUMERIK 840D Operate
- Siemens SINUMERIK 840D HMI Advanced
- Stäubli
- YASKAWA MOTOMAN
- AMT
- Atlas Copco Tightening Systems
- BOSCH Rexroth Tightening Systems
- COGNEX DataMan Scanner
- COGNEX In-Sight
- Danfoss VFD
- Fronius Welding Systems
- Kistler DMF-P
- Kistler maxymos
- Lenze 8400Protec
- SEW VFD
- SICK Scanner
- Siemens VFD
Documents
- Adobe PDF
- Allen Bradley Stratix
- ASCII
- AUVESY Image Service
- Binary
- CSV
- FTP, SFTP
- Hirschmann Belden
- Microsoft Excel
- Microsoft Word
- Network (UNC)
- Phoenix mGuard
- PC images with Acronis and more
- PC images with Drive SnapShot
- Siemens SCALANCE switches
- SSH
- XML
Achieve more certainty, clarity and security by identifying unauthorized program changes immediately, quickly finding the right data needed for disaster recovery and generating change records quickly and easily.